14) which of the following are breach prevention best practices
Access only the minimum amount of PHIpersonally identifiable information PII necessary. Ensure that your sensitive data is backed up regularly in case of a ransomware attack or system failure that causes loss of data.

Amulet Winery Investors Sue Tuck And Boo Beckstoffer Alleging Breach Napa Valley Wineries Meadowood Napa Valley Winery
10 The HIPAA Security Rule applies to which of the following.

. 10 The HIPAA Security Rule applies to which of the following. Which of the following are breach prevention best practices. Addresses three types of safeguards - administrative technical and physical.
Access only the minimum amount of PHIpersonally identifiable information PII necessary Logoff or lock your workstation when it is unattended Promptly retrieve documents containing PHIPHI from the printer All of this above correct 3 The minimum necessary standard. A Access only the minimum amount of PHIpersonally identifiable information PII necessary B Logoff or lock your workstation when it is unattended C Promptly retrieve documents containing PHIPHI from the printer D All of this above. Strong passwords are considered over eight characters in length and made up of both upper and lowercase letters numbers and symbols.
14 which of the following are breach prevention best practices. Protects electronic PHI ePHI c. Access only the minimum amount of PHIpersonally identifiable information PII necessary.
Convene a workgroup to research threats vulnerabilities. Logoff or lock your workstation when it is unattended C. Consider designating staff to carry out security monitoring.
All of the above. Which of the following are breach prevention best practices. Which of the following are breach prevention best practices.
Discuss best practices for preventing breaches. B- Logoff or lock your workstation when it is unattended. What of the following are categories for punishing violations of federal health care laws.
Established a national set of standards for the protection of PHI that is created received maintained or transmitted in electronic media by a HIPAA covered entity CE or business associate BA b. Out of the box AWS offers. Logoff or lock your workstation when it is unattended.
Access only the minimum amount of PHIpersonally identifiable information PII necessary B. Access only the minimum amount of PHIpersonally identifiable information PII necessary. Best Practices in Breach Prevention Develop appropriate security measures Monitor compliance with required measures Comply with reporting requirements W.
A- Access only the minimum amount of PHIpersonally identifiable information PII necessary. 2 Which of the following are breach prevention best practices. What are breach prevention best practices.
Remediation Accessed N PHI transmitted orally PHI on paper PHI transmitted electronically correct All of the above-----11 Which of the following are breach prevention best practices. Best Practices for Enterprise Cloud Security. Promptly retrieve documents containing PHIPHI.
All of the above answer a. Remediation Accessed N PHI transmitted orally PHI on paper PHI transmitted electronically correct All of the above-----11 Which of the following are breach prevention best practices. Which of the following are examples of personally identifiable information PII.
A breach as defined by the DoD is broader than a HIPAA breach or breach defined by HHS. Since cloud security is not widely understood it may be difficult to delineate it in the context of more general information security. 3 2015 Definitions.
20 Which of the following are breach prevention best practices. S3 Breach Prevention. When a data breach occurs involving a cloud service the impulsive reaction is to denounce using the cloud at least for sensitive information.
Best practices for incident response plans the first 24 hours following a breach questions reputation. Here are 10 best practices that organizations can use when developing data breach prevention methods and incident response plans. Protect your most critical digital assets by segregating them and prioritizing them in your business continuity plan.
Breach prevention strategies TheftLoss.

The Parent Toolkit App Text Toolkit To 33733 To Get The App On Your Mobile Device Now The Parent Toolkit App Is Designed To Help You N Technology Pinte

Situational Analysis Of 10 Countries With A High Burden Of Drug Resistant Tuberculosis 2 Years Post Unhlm Declaration Progress And Setbacks In A Changing Landscape International Journal Of Infectious Diseases

The Job Of Dataprotection Is Getting Tougher Every Day And Minor Mistakes Can Cost Any Organization Thousands Of Dollars Data Loss Prevention Data Loss Data
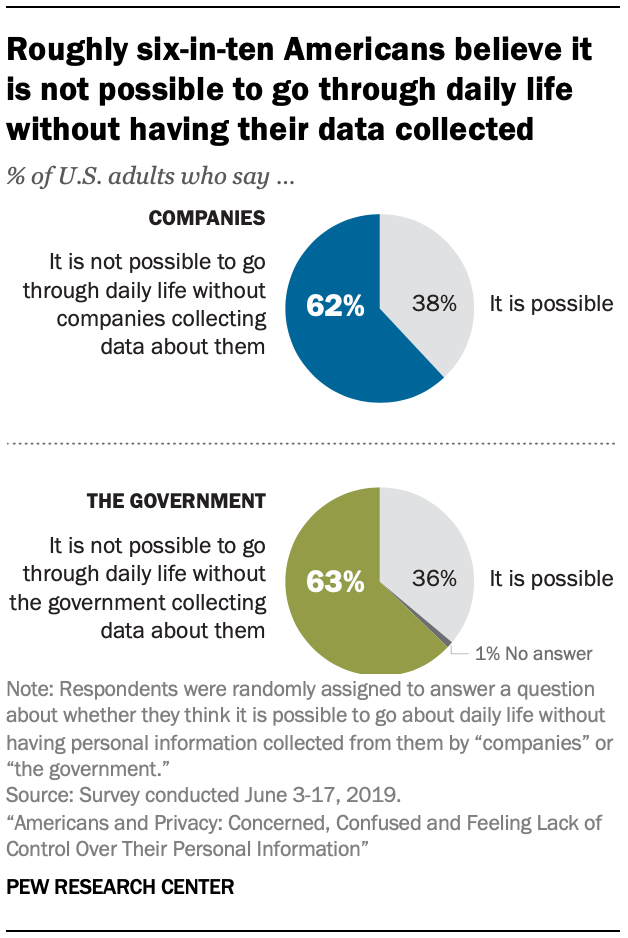
Americans And Privacy Concerned Confused And Feeling Lack Of Control Over Their Personal Information Pew Research Center

How Not To Greet A Dog 11 X 14 Kid Friendly Poster Zazzle Com In 2022 Dog Body Language Dog Biting Dog Language
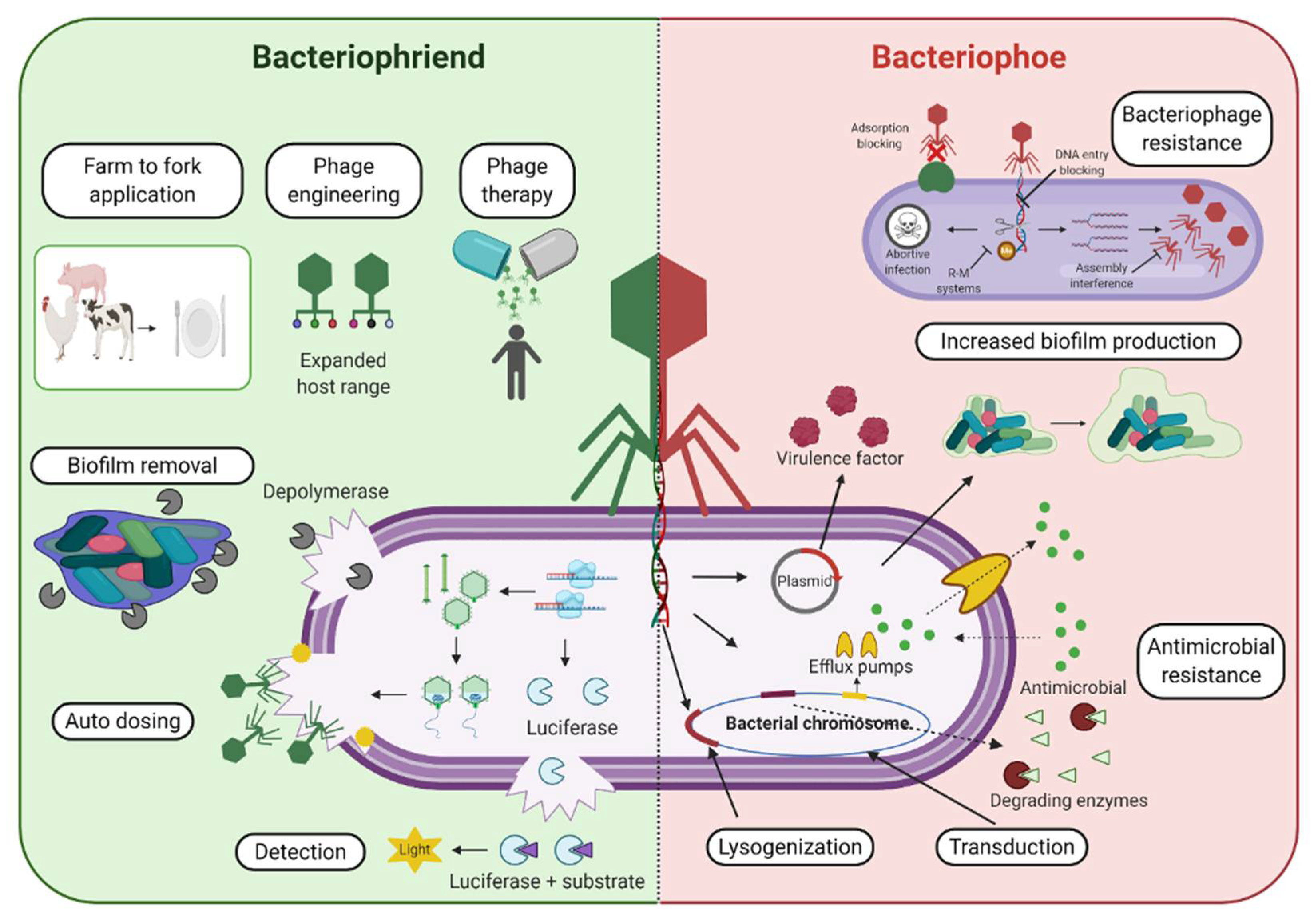
Pharmaceuticals Free Full Text The Age Of Phage Friend Or Foe In The New Dawn Of Therapeutic And Biocontrol Applications Html

What Is The Need Of Ip Addresses Restriction In Enterprises Understand The Importance Of Implementing Ip Add In 2021 Cloud Data Internet Protocol Address Ip Address

Jeannieborin On Twitter Yahoo News Sayings Finance

Guidesforbackup On Twitter Software Security Wordpress Security Cyber Security

Healthcare Information Security 5 Ways To Maintain In 2022

The Five Most Common Attack Patterns Behind Today S Data Breaches Tripwire Cyber Security Tech Apps

Fintech Inclusive Growth And Cyber Risks Focus On The Menap And Cca Regions In Imf Working Papers Volume 2018 Issue 201 2018

12 Ways To Protect Your Business From A Ransomware Attack Infographic Cybersecurity Infographic Infographic Cyber Security

Fintech Inclusive Growth And Cyber Risks Focus On The Menap And Cca Regions In Imf Working Papers Volume 2018 Issue 201 2018

Situational Analysis Of 10 Countries With A High Burden Of Drug Resistant Tuberculosis 2 Years Post Unhlm Declaration Progress And Setbacks In A Changing Landscape International Journal Of Infectious Diseases

4 Practical Techniques And Countermeasures To Battle Ransomware Carbon Black Prevention Cyber Security Optimization

Businessman Login With Fingerprint Scanning Technology Fingerprint Digital Lock Fingerprint Lock